Perusing the private address book and making live video calls — all from a locked iPhone 4.
Last time we explored how an incorrect time setting could expose your pictures on a locked iPhone. Today we’ll have a bit more fun.
Often when doing security work, you’re happy if you manage to leak just a single bit (yes, one binary digit) of encrypted material. That one bit could be the tip of the iceberg, so to speak, which might lead to more secrets underneath.
Lets see how many bits of personal information we can gather from a locked, passcode-protected iPhone 4, without jailbreaking or using any special tools?
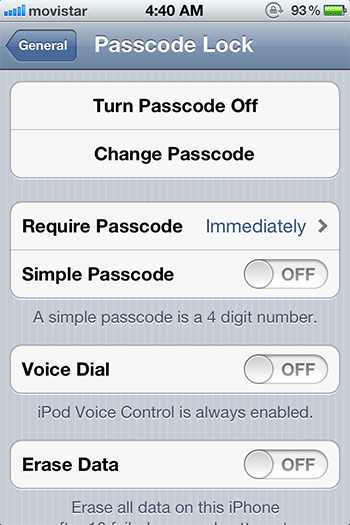
Below is a screenshot of my iPhone’s lock setup screen. The settings are rather conservative: a long passcode is required immediately; and Voice Dial is DISABLED (when the screen is locked).
Note: I’m using an iPhone 4 (not 4s) with vanilla iOS 5.0.1 (the latest at this time). I do not have Siri on this phone.
When the iPhone 3GS first came out, many were surprised that Voice Dial was enabled by default on their locked iPhones (and similarly, with Siri on the 4s). So for our exercise today, we made sure Voice Dial is turned off.
Voice dialing is accessed by long-pressing the phone’s home button. Again I’ve disabled voice dialing, but a fine print on the setup screen above notes that “iPod Voice Control is always enabled” so it can still be used to play songs, etc.
Can we trick this restricted Voice Control to leak some private info, and perhaps trick it to make calls for us? (Yes, we can!)
First let’s see how the Voice Dial restriction works. I lock my phone, then long-press the home button until Voice Control appears. I command it, “call <Alice>”. The phone responds with “Voice Dialing is disabled“. As it should. All good, right?
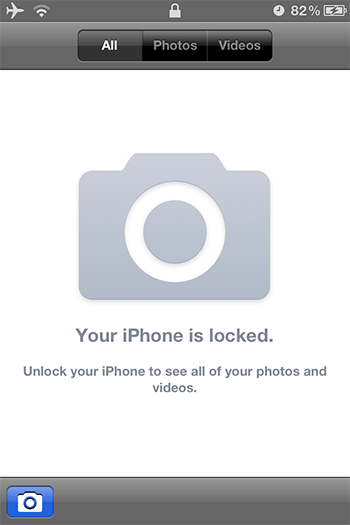
Now “slide to unlock” but instead of entering the passcode, hit the “Emergency Call” button (bottom-left). We get this special emergency call screen:
With this screen showing, I again bring up Voice Control, and repeat, “call <Alice>”. This time the phone responds with “No match found“. Hmm, different!!
Actually, that response in itself, my friends, is already a leak. Voice Control reveals that I don’t have a contact named “Alice” in my Contacts. One leaked privacy bit.
Just to test, let’s try with someone who’s actually in my address book, my friend Wayland. I bring up Voice Control again from the Emergency Call screen and say “call <Wayland>”.
 (Locked) Voice Control calling Wayland
(Locked) Voice Control calling Wayland
Wow, it tries to dial out! Although the call fails to actually connect, the screen reveals Wayland’s full name and that I have his mobile number. Not a huge deal, but more leaked bits!
At this point, it’s easy for anyone to enumerate through the Contacts by simply trying common first names like Adam, Bob, Charles, etc. Let’s see how far we can go.
Here’s an example when I say, “call <Lisa>”:
 Multiple matches shown for the name Lisa
Multiple matches shown for the name Lisa
Voice Control leaks that I have two Lisas in my contact list, one Lisa Atkins and one Lisa Klein**. Repeating with “call <Lisa Klein>” yields further information:
 Multiple numbers listed for Lisa Klein
Multiple numbers listed for Lisa Klein
Now Voice Control leaks that I have two numbers for Lisa Klein: her “mobile” and another number at the “love shack“. Had this been my jealous girlfriend probing my locked phone, I would’ve been totally busted!
Remember, we’re getting all this info from a locked phone with Voice Dial explicitly disabled.
So far we’ve only enumerated through the Contacts. Can we actually complete a call from the locked phone? With FaceTime, the answer is yes!
Again starting from the Emergency Call screen, this time I say, “FaceTime <Lisa Klein>”. And Voice Control dutifully connects, to the love shack, with full two-way video live streaming. Yikes! Not what I’d expect from my locked phone!
During testing, the FaceTime calls from my locked iPhone successfully connected and I was able to see + converse with the other party. The test calls disconnected after a few minutes, but those disconnections might be due to the spotty internet service here at my hotel in Medellín, Colombia.
Bottom line: We’re able to trick Voice Control to enumerate through the private address book and make live FaceTime video calls on a locked iPhone 4, even with Voice Dial specifically disabled in the settings.
**Some names faked to protect the innocent.
Special thanks to Wayland Chan for helping me test FaceTime.
p.s. I have not tested this issue on the iPhone 3GS, which has Voice Control but lacks FaceTime.
UPDATE: Feb 8, 2012: While the iPhone attempts to connect the FaceTime call, it will show the contact’s profile picture if any. So a stranger using your iPhone could possibly see pictures of your contacts even if they do not have FaceTime enabled.
UPDATE: Feb 9, 2012: CNET also tested the bug on the iPhone 3GS and the iPhone 4S.