I always get a bit antsy about hacking researching vulnerabilities when I travel, and this time is no exception. Often I notice “glitches” or abnormalities which I want to investigate, but since I’m in the middle of riding my motorcycle from Canada to Argentina, infosec has been on the back burner.
Recently I took advantage of great wi-fi in Costa Rica to finally upgrade my iPhone 4 to iOS 5. Double-clicking the home button now allows one to quickly access the Camera app even from a locked phone:
 The camera icon (bottom-right) is now accessible from a locked iPhone
The camera icon (bottom-right) is now accessible from a locked iPhone
Since the camera is locked, Camera app has a smart feature barring access to the iPhone’s album. You can only see pictures taken from the current (locked) session.
As an aside, I thought I noticed a glitch whereby I could completely bypass the passcode lock, but turns out it’s just poor UI from Apple. (There’s a state where the phone is locked but a passcode is not yet required, and the UI during this period can be misleading.) I changed the passcode setting to “immediate” after that.
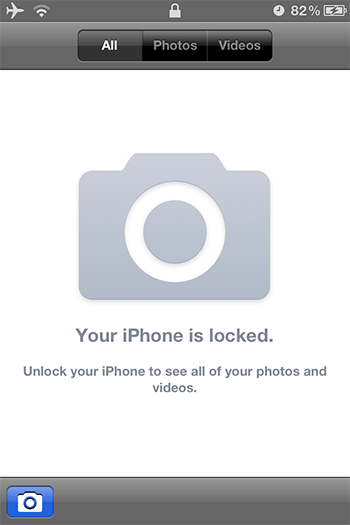 UI barring access to album pictures from locked phone
UI barring access to album pictures from locked phone
While researching the above “glitch”, I was intrigued at how the Camera app’s album manager was able to segregate your “protected” images vs. the ones from the current session. It’s like a “jail” for images. I wondered if I could break out of this image jail.
Turns out Apple’s restriction is just a simple filter based on the timestamp when the Camera app was invoked. You’re allowed to see all images with a timestamp greater than this invocation time. Yet that leads to an immediate hole: if your iPhone’s clock ever rolls back, then all images with timestamps newer than your iPhone’s clock will be viewable from your locked phone.
But time always moves forward, right? Why would your phone’s clock ever roll backwards?
- It could be due to user error. E.g., maybe while traveling across timezones you accidentally set the iPhone’s date or time incorrectly (rather than simply resetting the timezone). If you set the clock ahead of what it’s supposed to be, then this vulnerability will appear when you reset to the correct time. If you accidentally set the clock to the past, then your images will immediately become unprotected.
- It could be an iPhone glitch. E.g., a software or hardware issue could reset your iPhone’s clock to epoch time — iPhone’s “zero” time at midnight January 1, 2001. In this case all your images are exposed.
- It could be an infrastructure error. E.g., if you automatically sync from a erroneous external time source (cell phone company, etc.)
I don’t think normal (non-Apple) apps can change the iPhone’s clock, but if it can then that could be another possible source of rollback.
This vulnerability is simple to test. Just set your iPhone’s clock to a time in the past (say, in 2010). Then access the Camera while your phone is still locked. Lo-and-behold, you’ll be able to see all your “protected” images.
The point to all this is that Apple should not rely on a simple timestamp to restrict image access. Changing the iPhone’s clock — forwards or backwards — should not affect its security. We can’t guarantee the clock will always monotonically more forward, and when it doesn’t, the system should fail-secure.
In the big picture, if real “bad guys” have physical access to your phone, then the game is over already. However, as I wrote previously, defense-in-depth is a basic concept which should always be applied.
In various occasions I’ve advised clients to secure their time servers, etc., in the context of esoteric cryptographic attacks, audit logging, and other protocols which depend on accurate timekeeping. I’m a bit amused that the iPhone is vulnerable to a simple time change.
[…] tech consultant Ade Barkah has discovered a bug which allows photos on an iPhone running iOS 5 to be viewed via the lockscreen […]
[…] tech consultant Ade Barkah has discovered a bug which allows photos on an iPhone running iOS 5 to be viewed via the lockscreen […]
[…] 5 疑似存在相册泄露 bug加拿大科技顾问 Ade Barkah 在个人博客上披露出苹果 iOS 5 移动操作系统的一个bug: […]
[…] ermöglicht Zugriff auf Fotos trotzt Passwort Sicherung! iOS – Mittwoch, der 04.01.2012 um 10:09 UhrKanadische Technik Spezialsiten haben jüngst einen iOS Bug aufgespürt, der es in sich hat. Obwohl das iPhone Passwort geschützt […]
http://www.apfelnews.eu/2012/01/04/ios-5-bug-ermoglicht-zugriff-auf-fotos-trotzt-passwort-sicherung/
[…] fonte, via […]
[…] error fue descubierto por el consultor de tecnología Ade Barkah, en Canadá, quien demuestra que el bug surge efecto si la hora y/o fecha de nuestro dispositivo se […]
[…] Ade Barkah explains it further on his blog, […]
[…] Peekay.org via […]
[…] is visible even if the device is locked with a passcode. Technology consultant Ade Barkah has discovered a security/privacy vulnerability in Apple’s iPhone that leaks iOS 5 album photographs under […]
All you have to do is roll back the year, that is the issue. When you roll back the YEAR ONLY then you get access to Camera Roll and can delete images.
If you go forward in time to year 2013 it does not work.
If you change the date without the year it does not work.
it is only by changing the YEAR TO A PAST YEAR will this occur. Feel free to confirm this information.
Set your phone to the current year or make sure that automatic update of date and time is on until apple fix.
Thanks.
Thanks for the comment. It is not necessary to change the year. E.g., if the clock resets to Jan 1, 2012 then all pictures taken between Jan 1 and now will be exposed.
If the clock is incorrectly set ahead (say to 2013), then any pictures taken after that will have a timestamp in 2013. When the clock is subsequently reset to the correct time (back to 2012) then all those pictures will be exposed.
You are correct, looking at it on dev device which may be Beta. On a User device I can duplicate the issue. I stand completely corrected. If the Date and Time are rolled back than you get access to the comer roll. Nice discovery.
🙂
[…] 336 under post */ google_ad_slot = "4200351315"; google_ad_width = 336; google_ad_height = 280; Ade Barkah este cel care a descoperit un nou bug în iOS care ar permite oricărei persoane să vizualizeze […]
[…] Peekay.org (Ade Barkah's Blog), […]
[…] tech consultant Ade Barkah has uncovered a security bug in iOS 5 that allows for someone to bypass an iPhone’s lock screen and view the […]
[…] om de laatst gemaakte foto’s via een knop linksonder in het scherm te bekijken. Ade Barkah ontdekte tijdens een reis van Canada naar Argentinië dat dit systeem enkel gebruik maakt van het […]
[…] tech consultant Ade Barkah has discovered a bug which allows photos on an iPhone running iOS 5 to be viewed via the lockscreen […]
[…] consultant and iPhone tinkerer Ade Barkah has discovered a flaw within iOS 5 photo album security that will reveal locked photo albums should the clock on […]
[…] to researcher Ade Barkah Apple determines which photos can be viewed based on the timestamp of the photo relative to the […]
[…] Januar 2001 zurück gestellt werden, wären sogar alle Bilder auf dem Apple-Gerät frei einsehbar. Ade Barkah zeigt sich in seinem Blog erschüttert: “Das Verstellen der iPhone-Uhr sollte keine Auswirkungen auf die Sicherheit […]
[…] kanadische Sicherheitsexperte Ade Barkah erklärt, wie der nun entdeckte Bug von jedermann ausgenutzt werden kann. Laut Barkah genügt es bereits auf […]
[…] Comments « Incorrect time setting could leak iOS 5 album pictures […]
[…] via noodoproepfunctie Apple | The Initial | 10 februari 2012 om 11:15 Eerder was het al bekend geworden dat je vanaf een iPhone dat op slot zat foto’s kon inzien en nu blijkt dat je […]
[…] Bug de Acceso al carrete en iOS 5 por estación base falsa: Una de las características de iOS 5 es la posibilidad de utilizar el terminal como una cámara de […]